- SERVICES
- THREATS
- Sector-based threat landscape
- Agriculture
- Energy
- Maritime
- Manufacturing
- Technology
- Logistics
- Governments
- Country threat profiles
- Russian Federation
- China
- Iran
- North Korea
- United States
- Israel
- Threat actor profiles
- Fancy Bear/APT28
- Cozy Bear/APT29
- OilRig/APT34
- Charming Kitten/APT35
- Lazarus/APT38
- Double Dragon/APT4
- Sandworm
- Seaturtle
- Silent Librarian
- RESOURCES
- ABOUT US
- CONTACT
The Evolving Threat of OT: Do You Know Your Weak Spots?
As businesses become more connected, cyber threats are no longer just an IT concern — Operational Technology (OT) is increasingly a prime target. Considering these systems were initially designed to operate in isolation, they often lack the cybersecurity measures needed when linked to IT. This creates easy entry points for attackers, allowing them to move laterally between environments. Adding to the risk, OT systems are built for longevity. They often run outdated software that rarely gets patched, making them vulnerable. Given OT’s crucial role in power grids, manufacturing, and transportation, these systems have become an attractive target for cybercriminals and state-sponsored actors seeking to disrupt services, cause financial damage, or gain leverage.
In this three-part blog series, Hunt & Hackett has partnered with Xebia to explore OT security and raise awareness among C-level executives about its growing risks. With each instalment, we will dive deeper into the challenges and solutions shaping OT security today. The next parts will be released soon, stay tuned.
Traditionally independent, IT and OT systems are becoming increasingly interconnected, exposing critical vulnerabilities that cybercriminals are quick to exploit at scale. To date, 76% of industrial firms have experienced at least one attack [1], with a third reporting six or more OT breaches in 2024 alone [2]. The financial and operational implications are mounting as these attacks become more common and severe. This article explores the growing OT threat landscape, the hidden dependencies that amplify vulnerabilities, and strategies to mitigate evolving risks.
The Growing OT Threat Landscape
The rise of cyberattacks targeting Operational Technology (OT) systems has become an urgent concern for industries worldwide. OT systems, which control critical infrastructure like manufacturing processes, utilities, and transportation, are increasingly under threat. Because primary business processes run on OT systems, it gives attackers more leverage than IT, making them an attractive target. Hacktivists, in particular, are very interested in attacking OT. Unlike other cybercriminals, their primary motivation is to make a statement by causing physical damage to critical infrastructure to draw attention [3][4].
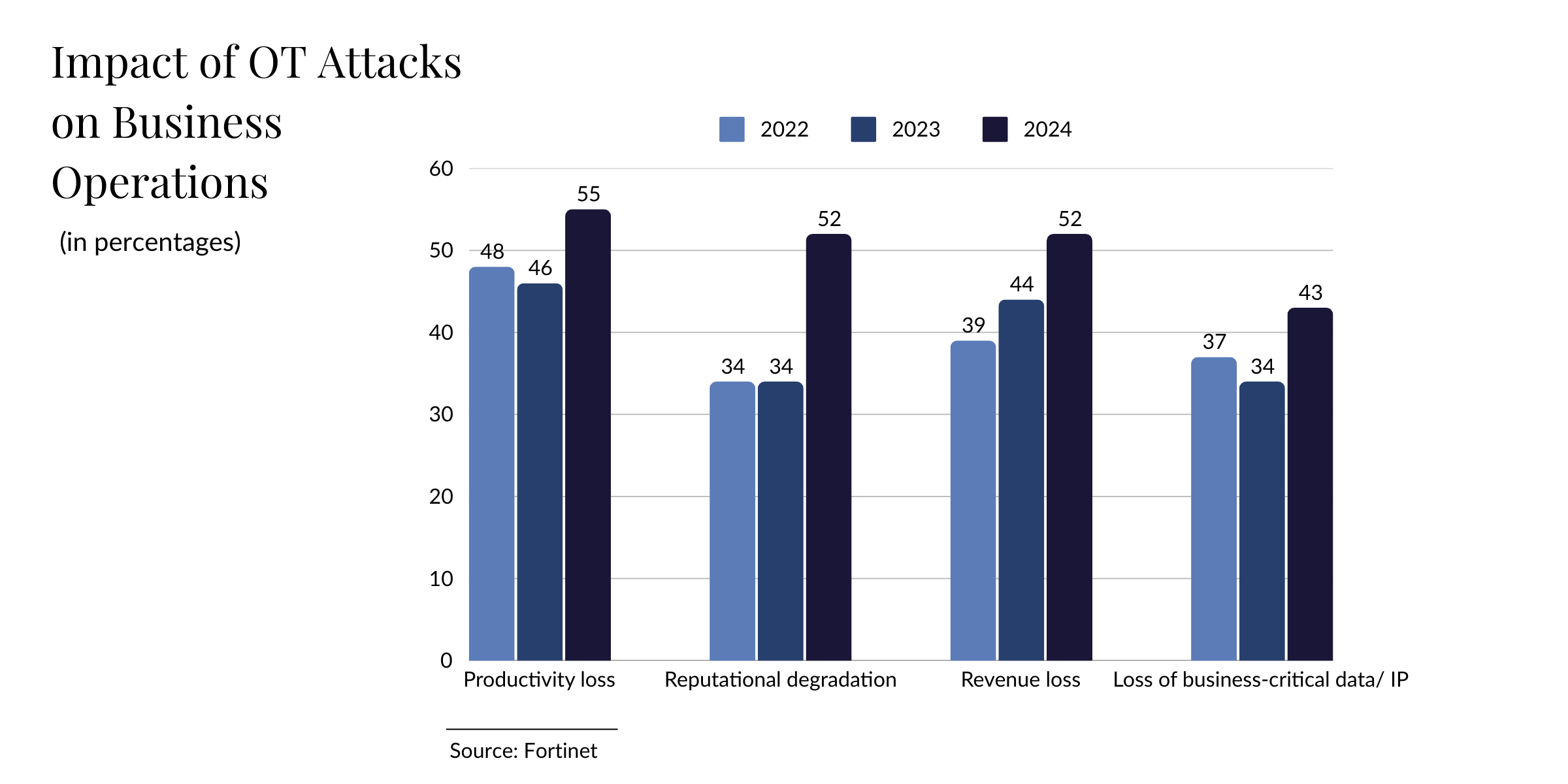
In 2023, 70% of OT professionals reported intrusions, a significant jump from 49% the year before [2]. These breaches often have far-reaching consequences. In that same year, 25% of OT attacks resulted in a shutdown of operations. Additionally, over half of the affected companies suffered productivity loss (55%), while 52% reported reputational damage and revenue loss [2]. These figures substantiate the leverage an attacker has when gaining access to the OT environment, disrupting immediate operations and long-term business performance. For example, a recent attack on 22 Danish energy companies severely affected operations [5]. Similarly, a U.S. water treatment plant breach compromised operational systems, jeopardising public safety and drawing significant attention to OT security vulnerabilities [6].
The nature of OT systems makes them uniquely vulnerable. Francisco Dominguez, Research and Innovation Lead at Hunt & Hackett, explains,
"Unlike IT systems, which prioritise Confidentiality, Integrity, and Availability (CIA), OT systems prioritise Availability, Integrity, and Confidentiality (AIC). This inverted order leads to different risk profiles, leaving OT systems less prepared for cybersecurity threats."
Core Issues
Increased Exposure
“OT was here long before IT was. However, its saving grace was that it was never connected,” says Filip Chyla, Security Consultant at Xebia. “Today, we expect that everything is interconnected, controlled remotely, and connected to the cloud. This means an active link between OT and IT now exists, significantly increasing the potential for exposure."
Hidden Dependencies
Considering most OT systems were not designed with interconnectivity in mind, they often rely on outdated protocols, making them highly susceptible when linked to modern IT networks. Unfortunately, these weak spots at the intersection of IT and OT, referred to as hidden dependencies, enable a breach in one system to escalate across both, causing major disruptions. Research shows that 72% of OT attacks originate in IT [1]. Chyla, "Numbers like these really underscore the importance of identifying the dependencies. But if you don’t know a dependency exists, how can you detect the risks it poses? That’s the challenge we face.”
In addition, there's also an architectural issue. Unlike IT systems, where access is carefully managed through methods like proxies or DMZs to limit exposure to the internet, OT systems often lack similar controls, leading to a flat architecture with no centralized gatekeeping, logging, or monitoring. This lack of segmentation means attackers can access the network through multiple points in the OT chain, undermining basic security principles like access control, detection, and response.
| Example 1, Access Control Systems |
|
| Example 2, IT-Dependant Billing System |
|
Hidden dependencies aren’t limited to internal systems — they also extend to suppliers and vendors, amplifying risks. For example, a manufacturer relying on imported components from China could face production disruptions due to trade restrictions. Finally, vendors and suppliers who have access to your systems can introduce additional vulnerabilities. Especially when weak or reused passwords are used across multiple customers, giving attackers easy access to critical assets.
Isolated and Outdated Systems
OT networks are typically isolated from corporate IT networks, making it harder to identify vulnerabilities or detect breaches before they escalate. Additionally, these systems are designed to operate over the entire lifecycle of the underlying physical asset. Even if they still function as intended, their technology quickly becomes outdated or unsupported, introducing numerous weak spots. Dominguez adds, “It is not uncommon for an OT asset, including its controlling hardware and software, to have an expected 20–30-year lifecycle. So, even if an OT system is still young, from an IT perspective, it is ancient. And even well-maintained OT systems will be at risk if connected to less secure OT systems within the same network."
Addressing Dependencies and Vulnerabilities
The evolving threat landscape for Operational Technology (OT) demands a proactive, integrated approach to security that unites IT and OT strategies. Here are three key steps to better protect your systems:
Risk Mapping
At the core of adequate protection lies a clear understanding of your critical business processes, associated risks, and the measures required to mitigate them. Proactive risk mapping helps organizations identify their most important assets and understand the dependencies that could become vulnerabilities. Real-time monitoring tools, such as Managed Detection and Response (MDR), play a pivotal role in detecting attacks at early stages, enabling swift action to minimize damage.
Prepare for Intentional Attacks
No security strategy can guarantee zero risk. Organizations must prepare for the inevitability of incidents by designing solid incident response plans that extend beyond business continuity measures intended for natural disasters. Dominguez explains, "A natural disaster does not have an intention. A flood or a fire just happens. A cyberattack is intentional — the attacker wants to achieve something. You will lose if you have built your risk management from a natural disaster perspective. Designing a security plan that considers malicious intent and focuses on measures like redundancy, secure backups, and response agility puts you in a position to respond to intentional and unintentional security issues.”
A Layered Strategy
Ultimately, prioritization is key. Security often takes a backseat to other business needs, but understanding and addressing your primary risks is paramount. While complete prevention is impossible, layered strategies —prevention, early detection, and effective response — form the foundation for resilience. By accepting that some risks cannot be eliminated, you can focus your resources on the areas that matter most, ensuring you are prepared for both the expected and the unpredictable.
References
- https://www.paloaltonetworks.com/content/dam/pan/en_US/assets/pdf/reports/state-of-ot-security-report-2024.pdf
- https://www.fortinet.com/content/dam/fortinet/assets/reports/report-state-ot-cybersecurity.pdf.com
- Waterfall, 2024 Threat Report
- https://www.nsa.gov/Press-Room/Press-Releases-Statements/Press-Release-View/Article/3761830/urgent-warning-from-multiple-cybersecurity-organizations-on-current-threat-to-o/
- https://therecord.media/danish-energy-companies-hacked-firewall-bug
- https://www.ssh.com/academy/operational-technology-breaches
- https://edition.cnn.com/2021/05/12/politics/colonial-pipeline-ransomware-payment/index.html