Cybersecurity for the Logistics sector
Over the past few years Hunt & Hackett has observed a discerning increase in the activity of Advanced Persistent Threat (APT) groups in the logistics sector. Logistics has long been the backbone of global trade, seamlessly connecting economies and ensuring the smooth flow of goods. But as the industry rapidly digitizes, it has become an increasingly attractive target for cyber threats.
One might not immediately assume that the logistics industry is a valuable target; after all, financial institutions have the money and government entities have the information hackers desire, right? Not quite. In fact, logistics companies manage vast amounts of sensitive data, and private and public entities depend on their operations every single day. These factors make them highly vulnerable to attacks.
How can you address this growing threat?
There is this legendary quote from Sun Tzu on how to overcome your adversaries: 'know thy enemy and know yourself; in a hundred battles, you will never be defeated'. To know your enemy starts with gaining an understanding of yourself, your threat landscape, your adversaries’ intentions, their modus operandi, and specific attacking methods. On this page, the cyber threats to the logistics sector are explored. Understanding the full picture of the challenges our clients may encounter helps us in doing what we do best: ensuring security for your business from specific cyber threats targeting your organization.
Request a free membership to access our full research insights
Already a member? Login here
Threat landscape
For the logistics industry
Advanced Persistent Threats (APTs)
Tactics, Techniques & Procedures (TTPs)
Attack tools
| Logistics | Logistics + related | Broader focus | All known | |
|---|---|---|---|---|
| APTs | 94 | 136 | 193 | 781 |
| TTPs | 1,674 | 1,998 | 2,458 | 4,109 |
| Attack tools | 1,474 | 1,577 | 1,996 | 3,616 |
Logistics faces more cyber threats than ever
To stay in control becomes increasingly difficult
Our proprietary threat diagnostic system shows a discernible increase in malicious activity targeting the logistics sector. As logistics companies race to keep up with rising global demand amid supply chain disruptions, cybercriminals are taking advantage of the pressure. If you operate in the sector, the risks of cyber-attacks, including intellectual property (IP) theft, ransomware, data breaches, and espionage, are escalating, especially if the appropriate defenses are not in place.
Actors and their motivation
The most active attack groups targeting the logistics sector are shown in the dynamic chart highlighting the relationships between the various threat actors, their motivation and their country of origin.
Knowing the APT groups, their motivations and origin countries provides a solid starting point for understanding what you are up against. To get a more comprehensive understanding of the threat landscape, it is important to research, map, and document your adversaries’ intentions to their modus operandi, attack methods and attack tools, as this provides more actionable information for strenghtening your defences.
More detailed information on the threat landscape for this sector?
Already a member? Login here
How it works
Threat landscape for the logistics sector
Our articles about the logistics sector
From Hunt & Hackett experts
Our approach
Controlling your cybersecurity risks
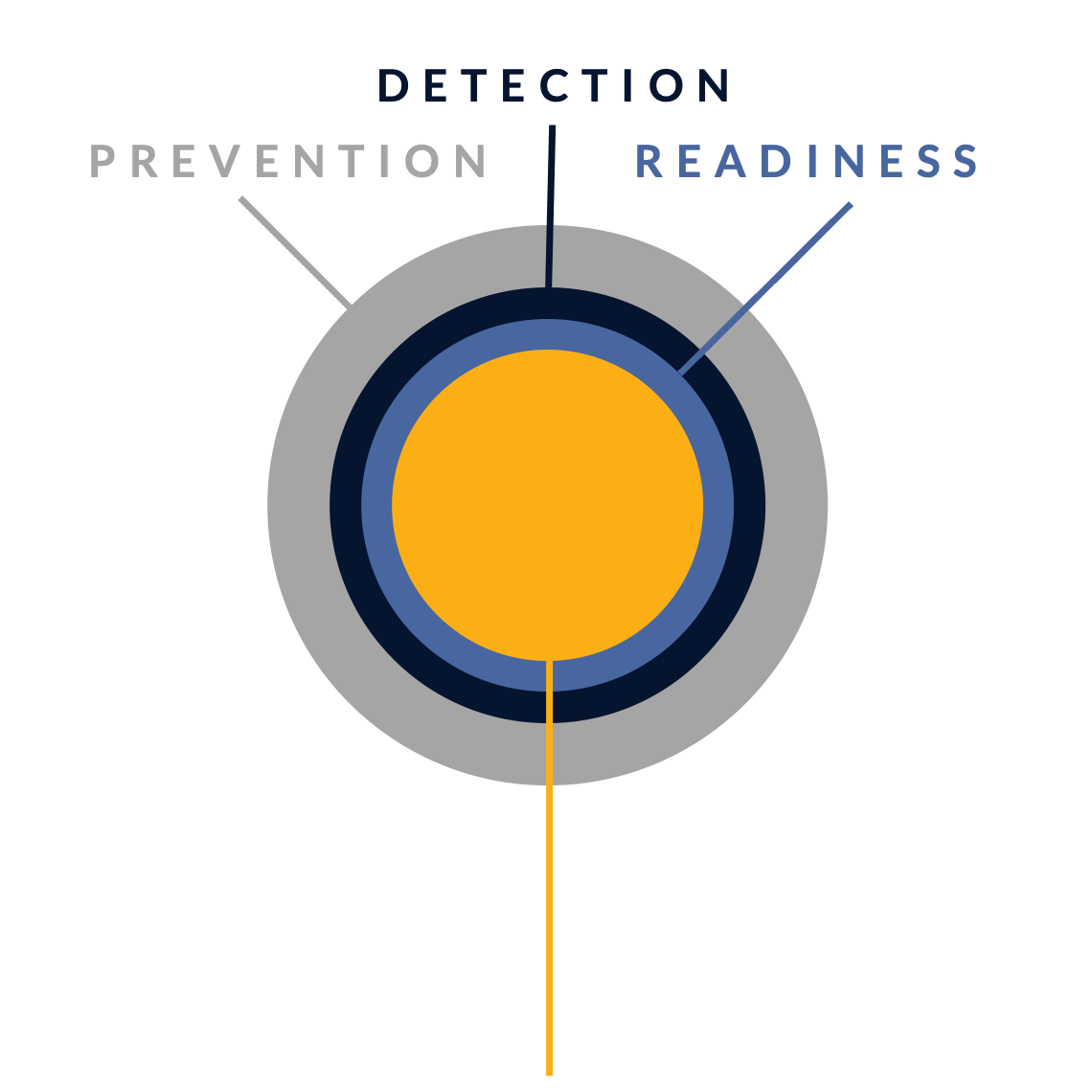
In their fight against cyber attacks, our customers typically go through several stages of maturity. By ramping up their prevention, detection and incident readiness over time – and optimizing this for their actual threat landscape – they reach a point where they have developed solid resilience against targeted attacks, with only highly controlled and accepted risks remaining.
There is no simple 'fix' to become resilient against the sophisticated cyber threats of today. Without serious resources or processes for systematic security activities, protection against modern cyber threats like ransomware is just a wish. Hunt & Hackett has developed a unique threat- and sector-driven approach to cybersecurity, enabling you to work from your current situation to a highly improved and controlled situation, optimized for your specific threat landscape and context as an organisation.
STAGE 1: Unknown risk
Pre-monitoring
-
STAGE 2: Reduced risk
Post-monitoring
-
Detection & response controls
Resilience against non-targeted attacks

STAGE 3: Controlled risk
Implemented roadmap
-
Resilience against non-targeted and semi-targeted attacks
STAGE 4: Highly controlled risk
Targeted attack resilience
-
Our services
Optimized for the logistics sector
Because we use your actual threat landscape and your sector as our starting points, our services are optimised for your specific context and needs.
Managed Detection & Response (MDR)
We detect & react to attacker activity in your environment, minimizing the impact on your business.
Security Program Gap Assessment (SPGA)
We assess your current security program, threat landscape, security controls and risk.
Incident Response (IR)
We help you manage a cyber crisis and contain security incidents, breaches and cyber threats.
Breach & Attack Simulation (BAS)
We validate your security choices by simulating attacks.